Quantum Computing Threat to Blockchain: What It Really Means for Crypto Security

When you send Bitcoin or Ethereum, you’re relying on math that’s been trusted for decades. That math is now under direct threat-not from hackers with powerful GPUs, but from something far more exotic: quantum computing. The scary part? It’s not science fiction anymore. We’re not talking about a threat 20 years away. We’re talking about a real, measurable risk that could rewrite the rules of blockchain security within the next decade.
How Blockchain Security Works Today
Every blockchain transaction depends on public-key cryptography. When you create a wallet, you get two keys: a private key (keep this secret) and a public key (shared openly). Your public key becomes your wallet address. When you sign a transaction, your private key generates a digital signature. Anyone can verify that signature using your public key-but no one can reverse-engineer your private key from it. That’s the magic. This system relies on problems that are easy to check but nearly impossible to solve backwards with today’s computers. For example, Bitcoin uses Elliptic Curve Cryptography (ECC), which depends on the difficulty of finding the private key from a public key. It’s like knowing a secret recipe and being able to bake a cake, but no one else can figure out the recipe just by tasting the cake. That’s where quantum computing changes everything.The Quantum Killer: Shor’s Algorithm
In 1994, mathematician Peter Shor invented an algorithm that runs on quantum computers. Shor’s algorithm can factor large numbers and solve elliptic curve problems in minutes-not years, not centuries. That means it can crack the private keys behind public addresses. Here’s the real problem: blockchain wallets expose their public keys during transactions. When you send Bitcoin, your public key becomes visible on the blockchain. If someone has a powerful enough quantum computer, they can take that public key and calculate your private key. Once they have that, they can sign transactions as you. Your coins? Gone. This isn’t theoretical. Researchers at Universal Quantum calculated in 2022 that breaking a Bitcoin signature would require a quantum computer with 13 million qubits. Sounds impossible? Maybe. But Google’s 105-qubit Willow chip in 2024 and D-Wave’s four-quantum-computer blockchain network show how fast the field is moving. The pace of progress is following a curve we’ve seen before: early computers were clunky, then suddenly, they weren’t.Why Your Bitcoin Isn’t Safe Yet-But Could Be Soon
Right now, quantum computers are nowhere near powerful enough to break blockchain encryption. But here’s the twist: we don’t need to break it today. We just need to collect the data and wait. That’s the "harvest now, decrypt later" attack. Imagine someone quietly recording every Bitcoin transaction ever made. They store the public keys, signatures, and addresses. Then, in 5 or 10 years, when quantum computers finally become powerful enough, they decrypt everything. All those coins? Stolen. This is why experts are alarmed. A Bitcoin transaction takes about 10 minutes to confirm. If a quantum computer can crack a private key in under 10 minutes, it can steal funds before the network even notices. The window is narrow-but it exists.
What’s Being Done About It?
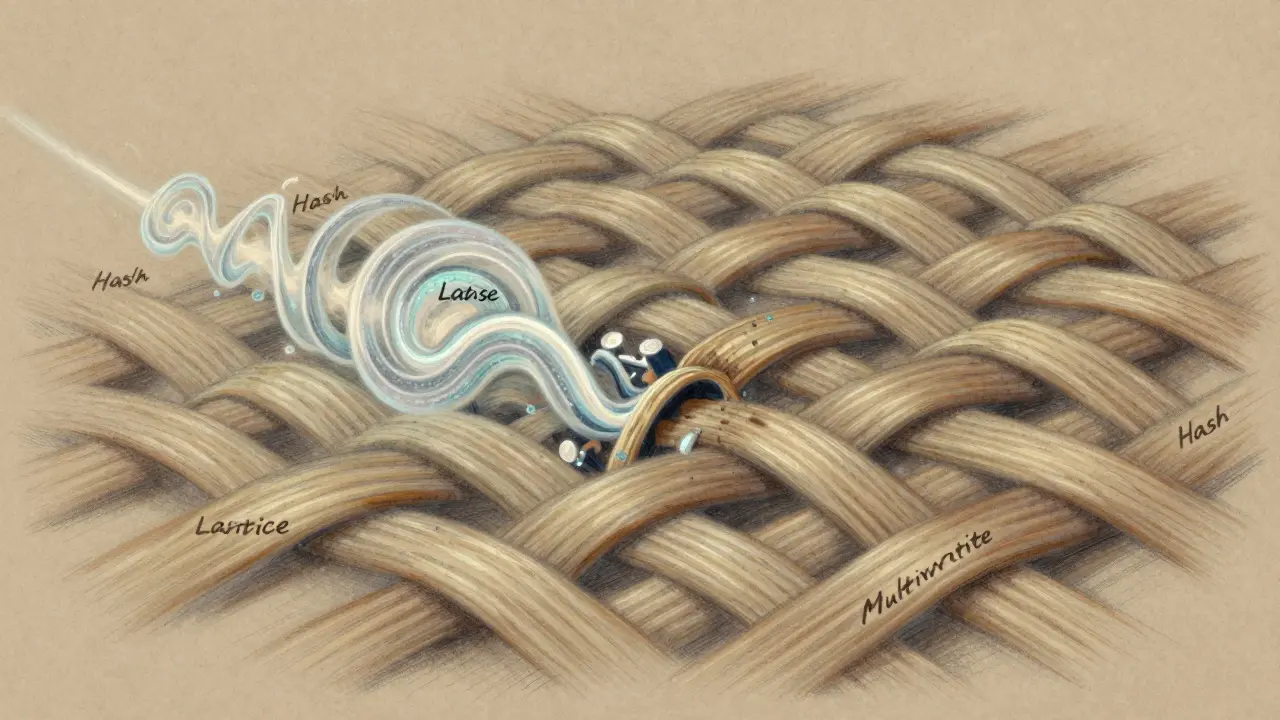
The blockchain world isn’t sitting still. Ethereum, Hyperledger, and other major platforms are already working on quantum-resistant upgrades. The goal? Replace ECC and RSA with algorithms that even quantum computers can’t break. These new methods include:- Lattice-based cryptography: Uses complex multi-dimensional math problems that remain hard even for quantum machines.
- Hash-based signatures: Rely on cryptographic hash functions (like SHA-256) that quantum computers struggle to reverse.
- Multivariate cryptography: Based on solving systems of nonlinear equations-another problem that’s tough for quantum algorithms.
What You Can Do Right Now
You don’t need to wait for a software update to protect your assets. Here’s what you can do today:- Avoid address reuse: Never send Bitcoin from the same address twice. Each time you spend, generate a new address. Most modern wallets do this automatically. If yours doesn’t, switch.
- Use newer wallets: Wallets that support Schnorr signatures (like those on Bitcoin’s Taproot upgrade) offer better privacy and are slightly more quantum-resistant.
- Don’t hoard long-term in old addresses: If you’ve had the same Bitcoin address since 2015, move your coins. The public key is already on the blockchain.
- Watch for quantum-ready chains: Projects like QANplatform, IOTA, and others are building blockchains from the ground up with post-quantum cryptography. Consider diversifying into these if you’re concerned about long-term security.
The Bigger Picture: It’s Not Just Crypto
This isn’t just a Bitcoin problem. TLS encryption, digital certificates, secure email, government records, and even your bank’s online system rely on the same math. If quantum computers break ECC and RSA, they break the entire digital trust infrastructure. That’s why governments and tech giants are pouring billions into quantum-resistant standards. The National Institute of Standards and Technology (NIST) has already selected four post-quantum cryptographic algorithms for standardization. The transition will take years-but it’s already started.The Timeline: When Should You Worry?
No one can say exactly when quantum computers will break blockchain encryption. Some experts say 2030. Others say 2040. But here’s the key insight: the threat doesn’t need to be immediate to be dangerous. The "harvest now" attack means the damage could be done today, even if the theft happens later. The race isn’t between hackers and blockchains. It’s between quantum progress and blockchain adaptation. The side that moves fastest wins.Final Thought: Fear Isn’t the Answer-Preparation Is
Quantum computing isn’t here to destroy blockchain. It’s here to force it to evolve. The same way the internet had to adapt to new threats like phishing and DDoS attacks, blockchain will adapt to quantum threats. The good news? We know the problem. We know the solutions. The only question is whether we act before it’s too late.Post Comment







so like... quantum computers are gonna steal my btc?? bruh i just bought some last week and now i'm paranoid. why does this feel like a movie plot??
also why is everyone acting like this is news?? i thought we all knew this was coming??
I mean, seriously, can we just acknowledge that this isn't a 'threat'-it's an inevitability? We've been dancing on the edge of this cliff for years, and now we're finally sliding over the edge. The public keys are already out there, recorded forever on the blockchain, waiting like a time bomb in a silent room. And guess what? The people who didn't move their coins from 2013? They're already dead money. They just don't know it yet. And no, switching wallets won't help if you're still using the same old addresses. You think you're safe? You're not. You're just in denial. And I'm not here to sugarcoat it.
I just... I can't believe we're here
Quantum computing. Like sci-fi made real.
My hands are shaking
Thank you for this comprehensive and meticulously researched overview. The urgency of transitioning to post-quantum cryptographic standards cannot be overstated. It is imperative that institutional actors, individual holders, and protocol developers collaborate to ensure the integrity of digital asset ecosystems. The window for proactive adaptation remains open, but it is narrowing with each passing day. We must act with diligence, not dread.
Ohhhhh so THATS why my crypto wallet app keeps asking me to "update security settings"? I thought it was just trying to upsell me more NFTs.
Also lol at people saying "just use new wallets"-like, sure, if you have 500 BTC in one address from 2014, you're just gonna move it?
Good luck with that, Karen.
The key point missed in most discussions is that quantum vulnerability applies only to public keys exposed during transactions. Addresses that have never spent from (i.e., only received funds) remain secure because their public keys are not revealed until spending. This is why address reuse is the real vulnerability-not quantum computing per se. The solution is simple: never reuse, use Taproot, and avoid legacy P2PKH addresses. No panic required.
So if I never spend my bitcoin its safe?
That's it?
Done
The entire discourse is fundamentally misinformed. We're not discussing quantum brute-force attacks-we're confronting the asymptotic collapse of NP-hard assumptions under BQP complexity class. Shor's algorithm reduces discrete logarithm problems to polynomial-time solvability via quantum Fourier transform, rendering ECC and RSA information-theoretically obsolete. The real issue isn't hardware scalability-it's the ontological fragility of classical cryptographic primitives in a post-classical computational paradigm.
So... we're all gonna die because of quantum computers?
cool.
my nfts are safe right?
they're just pictures lol
quantum? 🤯
so my dogecoin is gonna get hacked by a robot?
cool cool cool 😎
It's funny how we build systems on math we don't fully understand, then panic when the universe decides to change the rules. Maybe the real question isn't whether quantum computers will break crypto-but whether we were ever meant to trust something so fragile. The blockchain was supposed to be eternal. Turns out, so was the clock.
You people are still using Bitcoin? Bro.
It's 2025.
Anyone who didn't dump in 2021 is just a walking target.
And now quantum? LMAO.
Get a life.
I just want to say thank you to everyone who's working on this. It's easy to feel overwhelmed by tech like this, but the fact that people are building quantum-resistant chains, updating protocols, and educating users? That's hope.
Not every problem has a quick fix-but we're trying. And that matters.
The entire premise of this article is flawed. Quantum computing is not a monolithic threat. It's a collection of experimental systems with wildly varying architectures, error rates, and scalability limitations. The 13 million qubit estimate for breaking Bitcoin is based on theoretical models that assume perfect coherence and zero decoherence-a physical impossibility under current understanding of quantum mechanics. Meanwhile, classical computing continues to improve through architectural innovations like neuromorphic chips and optical computing. The narrative of inevitable quantum supremacy is a distraction, not a prophecy. The real risk is not quantum computers-it's the fear-mongering that distracts from more immediate threats like regulatory capture and centralized exchange vulnerabilities.