Future Protections Against Rug Pulls: How AI and Blockchain Analytics Are Stopping Crypto Scams
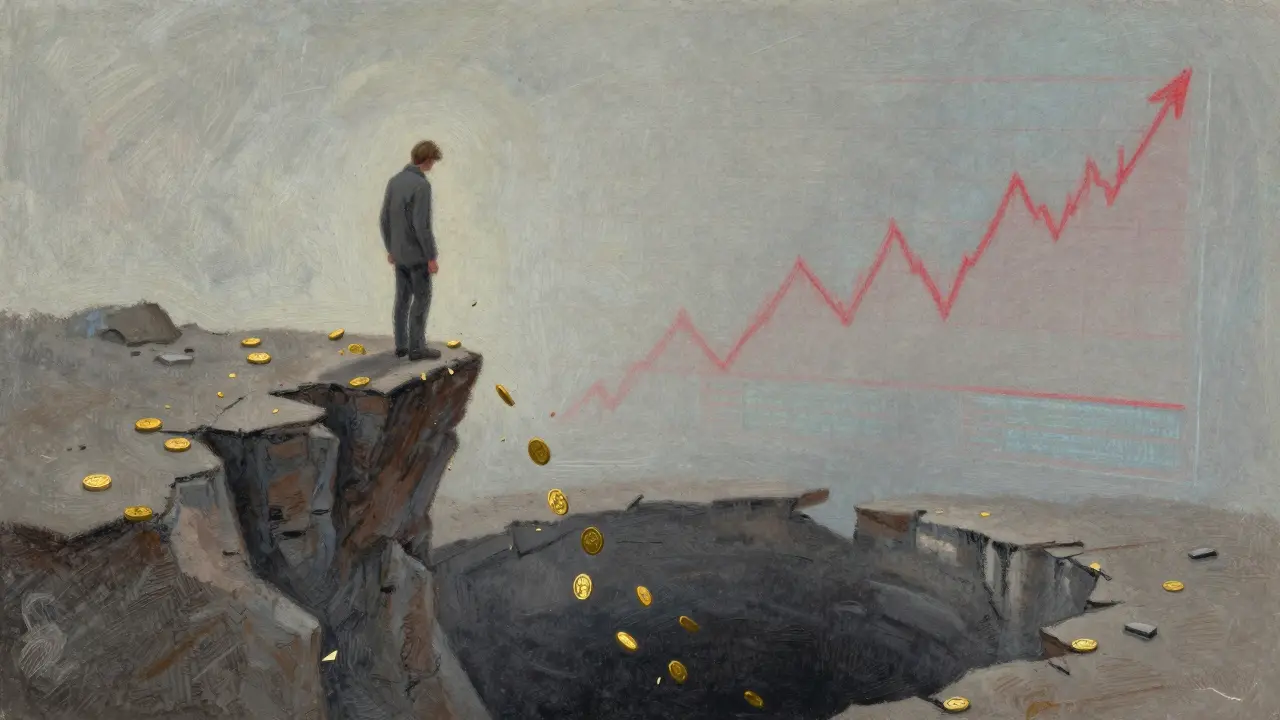
You click on a promising new token. The charts look green. The community is buzzing. You invest your hard-earned money, only to watch the value hit zero in minutes. This isn’t just bad luck; it’s a rug pull, defined as a malicious event where developers abandon a project or remove liquidity, leaving investors with worthless assets. In 2024 alone, U.S. citizens lost $9.3 billion to cryptocurrency scams, according to the FBI. But the landscape is changing. We are moving past the era of blind trust into an age of advanced detection.
The question isn't just how to avoid rug pulls anymore-it's how future technologies will make them nearly impossible to execute successfully. From AI-driven code analysis to behavioral tracking across blockchains, a new layer of defense is emerging. Let’s look at what these protections actually mean for you as an investor.
The Evolution of Rug Pull Tactics
To understand the future of protection, we first need to understand the threat. Rug pulls aren't random acts of chaos; they are industrialized operations. Scammers have moved from simple fake projects to sophisticated schemes that mimic legitimate ventures. There are two main types: hard rug pulls and soft rug pulls.
Hard rug pulls are sudden and violent. Developers deploy a contract, attract investment, and then instantly drain the liquidity pool. You can’t sell because there are no buyers left. Soft rug pulls are slower. The team stays active, provides updates, and maintains a false sense of security while quietly selling off their tokens over weeks or months. By the time you notice the price stagnating, they’re gone.
A particularly nasty variant is the liquidity sweep, which occurs when deployers provide initial liquidity for a memecoin, wait for users to trade, and then remove all liquidity once the pool's value increases. This is prevalent on platforms like Solana's Raydium V4. Research shows scammers often target pools with specific liquidity thresholds, executing sweeps on almost all available liquidity. If you’re holding a token in such a pool, you’re essentially sitting on a ticking clock.
RPHunter: The New Standard in Detection
The most significant leap forward in protecting against these scams comes from a novel technique called RPHunter, published in 2025 as an advanced detection system that integrates smart contract code analysis with transaction behavior monitoring using graph neural networks. Unlike older tools that looked at code or transactions in isolation, RPHunter understands that real-world scams involve a complex interplay between malicious code and suspicious trading patterns.
Here’s how it works. First, RPHunter analyzes the smart contract code to build a Semantic Risk Code Graph (SRCG). It looks for hidden functions, restricted sales, or unusual ownership rights. Simultaneously, it creates a Token Flow Behavior Graph (TFBG) by analyzing transaction data. It tracks who is buying, when liquidity is added or removed, and how funds move between wallets.
Using graph neural networks, RPHunter fuses these two data sources. The result? Exceptional accuracy. On a dataset of 645 manually analyzed rug pulls, RPHunter achieved a precision of 95.3% and a recall of 93.8%. When deployed in the wild, it identified 4,801 rug pull tokens with 91% precision. This isn’t just theoretical; it’s a practical tool that can flag threats before you even buy.
| Feature | Traditional Static Analysis | RPHunter (AI-Driven) |
|---|---|---|
| Data Source | Code only | Code + Transaction Behavior |
| Detection Method | Predefined patterns | Graph Neural Networks & Attention Fusion |
| Precision Rate | ~70-80% | 95.3% |
| Adaptability | Low (requires manual updates) | High (learns new patterns) |
Automated Safety Scores: Token Sniffer and GoPlus
Not everyone can read smart contract code. That’s where platforms like Token Sniffer, a platform that provides AI-driven smart contract analysis across multiple blockchains, generating safety scores from 0 to 100 based on code examination and liquidity status. come in. It simplifies complex security checks into a single number. A score above 80 indicates high reliability, while below 50 flags potential risks.
Token Sniffer doesn’t just look at the code; it evaluates holder distribution and liquidity locks. Is the top wallet holding 90% of the supply? Is the liquidity unlocked? These are critical red flags. Complementing this is GoPlus Security, which detects malicious addresses and decentralized application vulnerabilities, providing comprehensive security assessments beyond individual token analysis. Together, these tools form the first line of defense, allowing you to scan a project in seconds rather than hours.
Behavioral Analytics: Tracking the Scammer
Code can be obfuscated, but behavior leaves a trail. Companies like Elliptic, a blockchain analytics firm that offers automatic behavioral detection of scammer wallets and cross-chain risk detection capabilities to identify suspicious activities across multiple networks. are leading the charge in behavioral detection. Their systems monitor wallet movements in real-time.
If a developer wallet suddenly transfers large amounts to an exchange, it’s often a precursor to a dump. Elliptic’s tools flag these suspected scammer wallets automatically. This shifts the industry from reactive responses-chasing fraudsters after the money is gone-to proactive protection. Cross-chain detection is crucial here because sophisticated scammers move funds across different blockchains to obscure their tracks. By linking these behaviors, analytics firms can identify clusters of malicious activity that would otherwise remain hidden.
Holistic Evaluation: Token Metrics
Safety isn’t just about avoiding scams; it’s about identifying quality. Token Metrics, an analytics platform that assigns Trader Grades for short-term potential and Investor Grades for long-term viability, incorporating security factors like audit status and team credibility. takes a broader view. Their Investor Grade specifically weighs security factors alongside financial metrics.
This dual-rating system helps distinguish between legitimate projects with strong foundations and those exhibiting rug pull characteristics. By continuously analyzing thousands of tokens, Token Metrics identifies anomalies that individual investors might miss. It’s not enough for a contract to be safe; the project needs sustainable liquidity, credible team members, and transparent governance. This macro-level perspective helps you avoid not just scams, but also poorly managed projects that could fail for other reasons.

The Human Element: Discipline Over Fear
Technology is powerful, but it’s not a magic shield. The most effective defense combines advanced tools with disciplined investment practices. Never let FOMO (fear of missing out) override rational analysis. If a project promises guaranteed returns or uses pressure tactics, walk away.
Invest only what you can afford to lose. Conduct thorough research: check for security audits, engage with the community, and verify team credentials. Awareness of warning signs remains crucial. Future protection frameworks must educate users on recognizing red flags while providing tools that automate complex technical analysis. The goal is to create an ecosystem where informed decisions are easy to make.
Regulatory Oversight and Global Cooperation
Regulation is playing a growing role. The California Department of Financial Protection and Innovation maintains a Crypto Scam Tracker, documenting fraudulent platforms. These public databases help investors avoid known bad actors. However, the decentralized nature of crypto limits jurisdiction-specific regulations.
Future protections will rely on global cooperation. Information about scams needs to be shared across borders in real-time. As regulatory bodies collaborate, the ability to track and shut down illicit operations will improve. This doesn’t mean government control over every token, but rather a framework for accountability that protects consumers without stifling innovation.
Building a Multi-Layered Defense
No single metric provides sufficient protection. Effective rug pull detection requires synthesizing multiple indicators: smart contract code, transaction patterns, team credentials, liquidity stability, holder distribution, and social sentiment. Advanced platforms are developing holistic scoring systems that weight these factors appropriately.
Community-driven mechanisms are also gaining importance. Platforms that aggregate user experiences and expert reviews create collective intelligence. When one investor flags suspicious activity, algorithms can disseminate that warning rapidly. Reputation mechanisms will likely emerge, weighting reports based on the reporter’s track record of accuracy.
The challenge lies in balancing innovation with protection. Overly restrictive measures could stifle legitimate projects. Future frameworks must distinguish between complex, innovative contracts and malicious schemes. Machine learning models trained on extensive datasets of both legitimate and fraudulent projects will be essential for making these nuanced distinctions.
The future of rug pull protection is an ecosystem where technical tools, regulatory oversight, community reporting, and investor education work synergistically. While no solution can eliminate risk entirely, these layers dramatically reduce frequency and impact. By leveraging AI-driven detection, behavioral analytics, and disciplined research, you can navigate the crypto space with greater confidence and safety.
What is a rug pull in cryptocurrency?
A rug pull is a type of scam where developers abandon a cryptocurrency project or remove all liquidity from a trading pool, causing the token's value to plummet to zero and leaving investors unable to sell their assets.
How does RPHunter detect rug pulls?
RPHunter uses graph neural networks to analyze both smart contract code (Semantic Risk Code Graph) and transaction behaviors (Token Flow Behavior Graph). It identifies suspicious patterns by fusing these data sources, achieving high precision in detecting malicious projects.
What is the difference between a hard and soft rug pull?
A hard rug pull is sudden, with developers draining funds immediately. A soft rug pull occurs over time, where the team slowly sells off tokens while maintaining a facade of normalcy, gradually destroying the project's value.
Can Token Sniffer prevent me from losing money?
Token Sniffer provides a safety score based on code analysis and liquidity status, helping you identify high-risk projects. However, it is a tool for assessment, not a guarantee. Always combine its insights with your own due diligence.
Why is behavioral detection important for crypto security?
Behavioral detection tracks wallet movements and transaction patterns, such as large transfers to exchanges, which often precede rug pulls. This allows for proactive identification of scammers before they execute their plans.