Identity Verification to Prevent Sybil Attacks in Blockchain
You might have heard horror stories about someone farming hundreds of wallets to steal a $10 million airdrop. That isn't a glitch; it is a deliberate strategy known as a Sybil attack. As we move further into 2026, these attacks have become the biggest headache for any decentralized project trying to build a community. Everyone loves the idea of anonymous access, but total anonymity gives bad actors a free pass to rig the system.
Projects are now turning to identity verification systems as a shield. It sounds counterintuitive-using blockchain to track identities-but it is becoming the price of admission for security. In this guide, we will break down how identity checks stop bots, the trade-offs you face, and why privacy-preserving tech is changing the game.
Understanding the Sybil Problem
To fix a problem, you have to name it properly. A Sybil Attack is a security vulnerability where one malicious actor creates a large number of fake network nodes or identities to gain disproportionate control over a distributed network. The term comes from a 1973 book called 'Sybil,' which detailed the life of a woman named Shirley Ardell Mason who had dissociative identity disorder. In the blockchain world, this means one person pretending to be many different people.
Why does this matter? Imagine a decentralized autonomous organization (DAO) voting on whether to upgrade their protocol. If a single hacker can create 500 fake wallets, they can vote 500 times. They swing the vote, approve their own transaction, or drain funds from the treasury. Without identity verification, there is no way to distinguish a real person from a script running 1,000 virtual machines.
This vulnerability stems from the permissionless nature of public Blockchaina distributed ledger technology that records transactions across many computers so that the record cannot be altered retroactively. You can join without asking permission, and you don't have to show your ID. While this protects against censorship, it creates an open door for bot farms.
How Identity Verification Stops the Chaos
The solution seems straightforward: prove you are human before you participate. Identity Verificationthe process of confirming the authenticity of an individual's claimed identity using various data sources and technologies acts as a gatekeeper. When a project implements these checks, they tie a digital wallet address to a verified physical attribute, like a government ID or a unique biological marker.
In 2024 and 2025, we saw a shift from simple email confirmation to robust multi-factor checks. Modern systems often require:
- Biometric Liveness Checks: Using facial recognition to ensure a real person is present.
- Device Fingerprinting: Analyzing the hardware characteristics to flag bot clusters.
- Government Issued ID Validation: Matching documents against public registries to confirm legitimacy.
- Social Graph Analysis: Checking connections to other verified users to spot synthetic networks.
For example, during the Optimism airdrop event in 2023, users reported an average of 17.3 minutes spent verifying their identity. While annoying, this friction successfully kept bot farms from claiming millions in rewards that belonged to genuine users. The logic is simple: it costs too much time and effort to verify thousands of fake identities, so attackers lose interest.

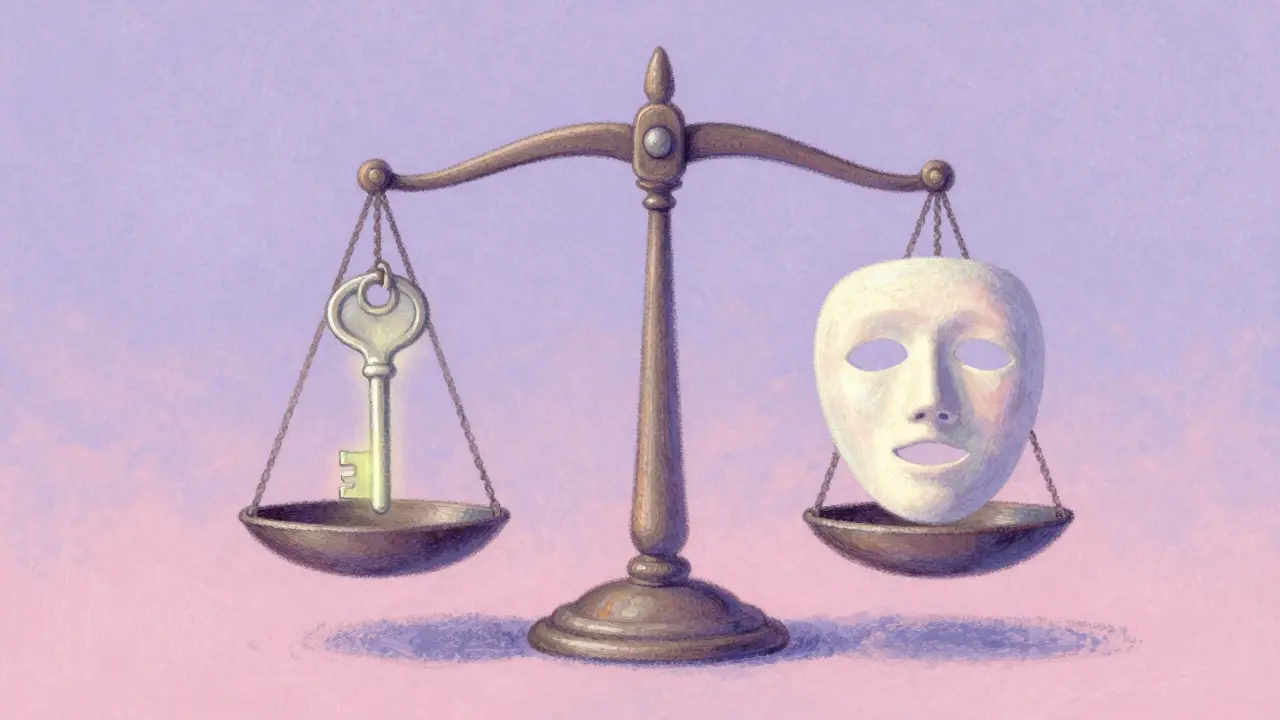
The Privacy Paradox
Here is where things get complicated. You cannot have it both ways easily. If everyone reveals their real names to participate in a decentralized network, what stops that database from being hacked? If identity verification becomes centralized, you undermine the core promise of blockchain, which is trustlessness.
Critics argue that mandatory Know Your Customer (KYC) rules turn permissionless networks into permissioned databases. Vitalik Buterin, co-founder of Ethereum, has historically warned that requiring identity undermines censorship resistance. He suggested that we should rely more on economic staking rather than personal data for security. However, as seen with DeFi protocols in 2023, purely economic solutions failed when token prices plummeted, allowing attackers to buy enough tokens to manipulate the system.
This brings us to the modern compromise: Zero-Knowledge Proofsa cryptographic method that allows one party to prove they possess certain information without revealing the information itself. These mathematical proofs let you prove "I am a real human" without revealing "My name is John." By 2026, this technology has matured significantly, allowing projects to issue a "Unique Human Token" on-chain that verifies uniqueness without exposing personal documents.
Implementation Strategies for Projects
If you are building a DAO or a DeFi platform, integrating identity verification is no longer optional for high-stakes environments. There are two main paths developers take in 2026.
| Method | Security Level | User Privacy | Cost |
|---|---|---|---|
| Centralized KYC | High | Low | $$ |
| Decentralized ID (DID) | High | Medium | $$$ |
| Social Recovery | Medium | High | $ |
| Proof of Humanity | Medium | High | Free |
Many enterprises prefer Digital Identity Walleta secure storage application for digital credentials that allows users to store, share, and manage verifiable credentials frameworks, such as those introduced by the EU in 2023. This allows organizations to accept credentials issued by banks without storing the raw data themselves. It reduces liability and fits better with global regulations.
On the other hand, grassroots communities favor protocols like Worldcoin or Gitcoin Passports. These tools aggregate signals (like Twitter follows, GitHub commits, and ENS domains) to score your "human-ness." It is less strict than a passport check but effective enough to stop obvious spam. According to surveys from late 2023, 63% of new DAOs adopted some form of these signals for governance participation.
Real-World Impact and Case Studies
Let's look at how this plays out in practice. In the supply chain sector, Hyperledger Fabric networks already mandate verified identities because participants are known companies, not strangers. For these networks, Sybil attacks aren't a concern because the network is permissioned from day one. Security teams spend weeks implementing enterprise-grade identity management, ensuring every node operator is a legal entity.
Public networks face a harder challenge. Formo, a verification provider, reported processing 12,000 daily verifications with 98.7% accuracy in Q3 2023. Their data showed that most failures came from inconsistent government ID formats rather than actual fraud attempts. This highlights a major pain point: global identity documentation varies wildly. A driver's license from Perth might not parse correctly alongside a voter ID from Jakarta.
Another critical use case is protecting liquidity pools. If a new DeFi app offers high yields, sybil bots usually swoop in to claim the "free money," then exit immediately. By requiring a verified wallet interaction history, platforms can filter out fresh wallets created just for the exploit. It forces the attacker to age their wallet and build reputation, increasing their operational cost.
The Future of Trust
Looking ahead to the rest of 2026 and beyond, the lines between Web2 and Web3 identity are blurring. We expect the W3C Verifiable Credentials Data Model 2.0 to become the standard. This specification enables privacy-preserving claims where you can prove you are over 18 or a resident of a country without proving which age bracket you fall into specifically.
The MIT Digital Currency Initiative noted in 2024 that no solution perfectly balances three goals: Sybil resistance, privacy preservation, and permissionless access. Currently, we have to pick two. Most likely, hybrid models will win. Public chains will keep their open access for basic transactions, but layers above the base chain-like governance apps or social media-will demand verification tiers.
For developers in Perth, London, or Tokyo, the takeaway is clear. Building a product that is completely anonymous makes you vulnerable. Building a product that demands full KYC drives away users. The sweet spot lies in verifiable credentials that grant access rights based on proof of uniqueness, leaving personal data private. As the industry matures, ignoring this balance could mean losing your entire user base to sophisticated bot farms.







I think this is exactly what we needed to discuss right now the risk of sybil attacks is getting too high. I work in secuity and I see people tryign to game every new drop with farms of bots. It feels like the early days of email spam but much harder to catch because they hide behind crypto anonymity. If we dont fix verifiction soon the whole trust model collapses under bad actors. We need to stop pretending total privacy is worth the cost of losing real users.
totally agree with you here :)
i mean if bots take everything whats the point of building :D we need some checks but please keep it private
The balance between security and freedom is delicate. Many developers feel trapped between compliance and community trust. I understand why users resist handing over biometrics. Yet allowing fraud to thrive hurts the honest participants most.
One must acknowledge that the current state of affairs represents a catastrophic failure of decentralized governance ideals. It is simply unacceptable that malicious entities operate without consequence in these digital spaces. We observe that the proponents of absolute anonymity are effectively enabling financial theft on a grand scale. This situation demands immediate intervention through rigorous identity protocols. The suggestion that economic staking alone solves this is intellectually dishonest given the volatility of markets. Real humans deserve protection from algorithmic predators disguised as peers. Therefore, projects ignoring identity verification are fundamentally negligent towards their user base. We cannot continue to tolerate systems where a single script holds power equal to thousands of individuals. The path forward requires a hard shift towards verified human participation. Anyone opposing this transition is prioritizing convenience over integrity.
While the sentiment is understood there is nuance regarding implementation costs that small teams struggle with. Large enterprises can absorb the expense of KYC but indie devs cannot. We should focus on low friction solutions like passport integration.
Identity verification is essential.
ZKPs are the only viable vector for scaling trust without centralization overhead. Most legacy methods fail under load. Merkle tree aggregation offers better throughput than standard API calls.
Stop pretending ZKPs solve the data collection upstream problem. They just hide it better. People lie about who they are even before encryption. We need soulbound tokens or nothing else matters.
You guys really dont get it do you. Your personal data is already gone. Giving it to a centralized verifier is worse. But honestly you all deserve to lose your funds if you cant manage simple ID docs.
bros actually thinks giving bio data is safe lmao 🙄 blockchain is still better. we gona leak wallets soon. trust the tech not govt databases. i know lots about crypto and this is just basic stuff 🚀
They want your face and fingerprints to control your assets 🤖💰. It's a trap. Always has been. Wake up sheeple. Privacy is dead anyway. Why give them more ammo? 👁️🗜️
We must consider the deeper philosophical implications of quantifying human existence within a cryptographic ledger. When we define the self through algorithms we alter how society perceives value and interaction. The tension lies in our desire for connection versus our need for security boundaries. History shows us that centralization creeps in whenever efficiency becomes the primary metric. Yet decentralization suffers from its own inefficiencies that invite exploitation. Perhaps the answer isn't binary choice between open and closed but rather a layered approach where identity remains portable. We see glimpses of this in emerging standards but widespread adoption requires cultural shifts beyond mere technical specifications. Users need education on what they are trading away for safety guarantees. Without understanding the mechanism compliance fails to generate organic support. Trust is rebuilt slowly through transparent failures rather than perfect promises. We stand at a precipice where the wrong move fractures the ethos of the web entirely. It is incumbent upon us to weigh these factors with extreme caution and deliberation before mandating systemic changes. The collective well-being depends on finding equilibrium between access and accountability.
This perspective highlights the ethical complexity perfectly. Small steps are better than large jumps.
Sadly most people in this thread ignore the supply chain risks mentioned earlier. They focus on airdrops while enterprise gets breached daily. You prioritize fun over function which is tragic for industry growth.
It is true that retail care less about logistics than governance though. We need to educate communities on long term impact. Great breakdown of issues 😊
UK regulatory frameworks already cover DID extensively unlike US fragmented laws. European Digital Identity Wallets offer superior interoperability compared to American ad hoc models. Sovereign states should dictate standards not token issuers.
National borders create silos which break permissionless ideals. We need global protocol agnostic standards not regional walls. Fragmentation helps censors not users.